Your Web Security
This presentation is an HTML5 website
Press → key to advance.
Having issues seeing the presentation? Please use Google Chrome
Presentation by Coddict
Slides controls, press:
- ← and → to move around.
- Ctrl/Command and + or - to zoom in and out if slides don’t fit.
- T to change the theme.
- 3 to switch to 3D Mode
Your Web Security*
Protecting yourself from next-generation hackers
*Browse the internet securely without falling for the traps they might set you up for.
Coddict For Web Development
Who are we ?

Frederic Haddad
Coddict (Canada)
E-mail: freddy@coddict.com
freddyhaddad.com
Twitter: @freddyhaddad

Dany Moussa
Coddict (Lebanon)
E-mail: dany@coddict.com
danymoussa.com
Twitter: @danymoussa
Coddict For Web Development
What do we do ?
- Web Application development
- Web Security
- Web Servers Architechture
- Scaling Web Applications
- Web Design
- Web Marketing
- Search Engine Optimization
- IT Consulting
Table of contents
Unsecurity of wireless networks
Someone could be connected to your Wi-Fi Router
How to avoid it ? Knowing it's possible is the first step
Public networks...What's the danger ?
Whenever you connect to a wireless connection that is not yours, you are connecting to a public network. Schools, Universities, Cafes, Airports and Events have public wireless networks that are used everyday.
The first step that a hacker has to do to begin his hacking strategy is get access to the same network as yours. If he's in a public place, and you are both connected to that same Wireless network, that first step is already done.
Private networks...Not so secure afterall
Network connections that you own (such as your internet connection on your router at home) are private networks, which are meant to be used by only you.
Not to say that there aren't ways to make them secure, but some people nowadays still forget to protect their wireless networks using passwords/keys (such as WPA2).
Even those who protect their wireless networks sometimes use weak algorithms such as WEP/WPA-PSK which can be broken in 5 minutes today (using a software such as aircrack).
For similar reasons, at least 35% of private wireless networks are still easily accessible by a hacker with minimal effort.
In Summary...
 All the hacker needs to begin his hacking process is to be on the same network as yours.
All the hacker needs to begin his hacking process is to be on the same network as yours.
If you're at home and you don't protect your wireless network seriously the hacker can join the network. If you're in a public place, both of you most probably have access to the same public network.
Man in the middle Attack
A Devastating attack
Can take control over a network, spy on it, even completely freeze it
Man in the middle Attack: Why does it work ?
"The protocols that support network communication, which are relied upon for the Internet to work, were not specifically designed with security in mind" - Hacking: The next generation
Like caller IDs and e-mail communication, network communication is based on trust. So messages on the network are trusted by default. This means that if the hacker sent messages on the network while lying about it's identity, other devices will believe his identity anyway, so the hacker can impersonate other devices on the network!
Man in the middle Attack: How does it work ?
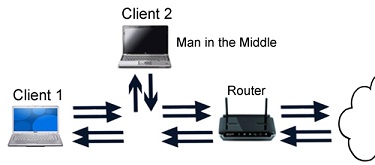
Since the network works based on trust, and that a hacker can impersonate any other machine on the network, two impersonations are everything a hacker needs to do to launch a man in the middle attack between a victim (user) and the router.
All the hacker needs to do is convince the router that he is the victim, and convince the victim that he is the router. Then the router will send him all messages dedicated to the victim, and the victim will send all messages dedicated to the router (the internet) to the hacker. He will then be standing in the middle of the communication between the victim and any other machine.
Man in the middle Attack: How does it look ?
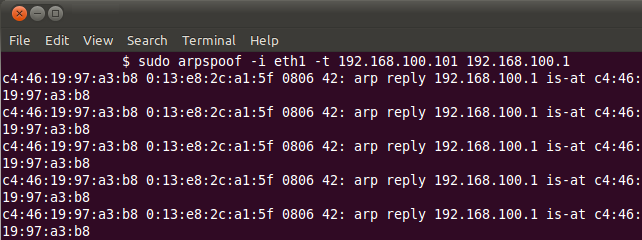
This is how it would look like if you were on a hacker's screen, impersonating the user and the router and becoming a man in the middle.
In this particular example, the tool "ArpSpoof" is being used to fake the computer's identity on the network and impersonate other devices.
What information does this reveal ?
Since network communications are all passing by the hacker, the hacker can read anything happening on the network, or even alter it.
This includes login information, banking information, chat conversations and even e-mails sent and received!
Other than the sensitive information that can be read, pages can be altered and changed when requested by the victim. So if the victim requests facebook.com, the hacker can show him a fake/hacked facebook.com lookalike that is unsecure.
But hackers can only practically read and use this information if it's being transferred unencrypted (HTTP) and not secured using SSL for example (HTTPS which is HTTP Secure).
How the hacker sees your account information
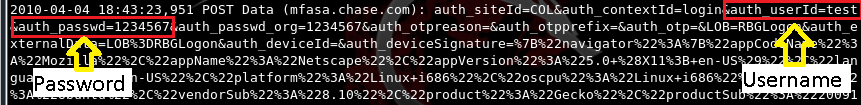
This is a picture showing how a hacker would probably see your login information. This text would appear to him once you login onto a website.
In this particular example, this information was captured by a python tool called "SSLStrip".
Serious consequences
Thinking of the possibility that any account can be compromised and e-mails read, this opens up a great array of consequences.
If bank accounts are stolen, your money can be stolen. If your university account is compromised, someone can drop you out of your courses.
If your social accounts are stolen someone can impersonate you. If your e-mail is stolen, any of your accounts can be reset.
For example, if a business CEO was browsing at a cafe and his e-mail login was stolen, it is then possible to spy on him and on the company's future decisions, this gives an unethical advantage to his competitors, and you don't want to be that CEO.
HTTPS and importance of SSL in online browsing
HTTPS is a combination of the HTTP Protocol with the SSL/TLS protocol to provide encrypted communication and secure identification of a network web server.

You can make sure you are browsing under HTTPS if you see at the beginning of your address bar "https://". Most browsers will also display a lock icon near the web address bar.
If you are browsing under HTTPS and you see a lock, this means 2 things: First that you are connected to the real website, and second that there is no one launching a man in the middle attack on you, and no one trying to compromise you. So you should keep making sure that you're browsing under https as much as possible, if you aren't, someone can compromise you using a man in the middle attack.
Basic precautions for avoiding being a victim
First of all, start by always checking that you're browsing securely (HTTPS), on sensitive login pages such as your bank website, GMail login page, or other sensitive pages where you might type sensitive information and passwords.
To make sure to always browse securely on sensitive pages build the habit of typing it in the address bar yourself, that way you can't miss it; Example: Instead of typing facebook.com or www.facebook.com, type the full "https://www.facebook.com" and check for the lock or the "https://" after you open it.
If something wrong was detected, you will usually see a red cross. This indicates that the connection isn't really secure and you could be victim of a man in the middle attack. This is an example of how it would look like on Google Chrome if an attacker was intercepting your communications on HTTPS:

Client Side Threats
Is this familiar on your Facebook Wall/Feed ?

Your friend didn't post it, he just fell for a client side threat and was tricked to post it on your/his wall.
Client Side Threats resulting from the man in the middle
If a hacker has launched a man in the middle attack, the most prominent way for him to make a client side threat is to modify the page content.

The above picture is an example of a Facebook.com page altered by a hacker. Anyone browsing Facebook on the network will see this message. Once the user clicks "Update Now", a trojan horse or a virus hosted by the hacker will be downloaded to the user's PC, sometimes granting the hacker full access to the user's PC.
Client Side Clickjacking
Check out this example. You must have a Facebook account to try it out. If you are not logged into your Facebook account, login first on Facebook.com and then Click Here to refresh this slide. If you are already logged into Facebook double click the small "DblCli" button below and then check out your Facebook Wall.
DblCli
DblCli
Client Side Clickjacking Explanation
This is the explanation to how the clickjacking was done:
DblCli
A Facebook Like button was put in front of the "DblCli" button, but it was put transparent. In the above example however, the Like button is not completely transparent for explanation purposes.
The user thinks he is clicking the "DblCli" button while he is clicking the transparent Facebook Like button in front of it. This is how the click was stolen from the user.
Now stealing a click on a Facebook like button is not a major issue but imagine if that button was a button that sends out money from your bank account, that would have a lot more serious consequences.
Javascript Social Engineering
Javascript is the programming language of the web. Some people think that Javascript is dangerous and disable it, but this is wrong, Javascript is not dangerous if you take certain precautions.
Javascript code can do any action you can do with your mouse and keyboard on a webpage. Usually Javascript code written inside a page is secure.
However you should not trust Javascript code that someone else gives to you, because he can write any action inside the code. When someone tells you to paste something in the address bar, and it begins with "javascript:", this is Javascript code. Just don't paste it in that case, because if you do, you're letting him do actions on your part through the code he wrote.
When people on Facebook fall for these Javascript Social Engineering, the code they paste usually sends a message and posts a link to all their friends, that's how those useless spam posts propagate on Facebook for example. Bottomline: don't paste anything in the address bar that starts with "javascript:" and you'll be fine.
Final Thoughts
During this presentation we briefly presented one of the most devastating network attacks that we are exposed to everyday: The man in the middle attack.
The goal of this presentation was to raise awareness to this attack. We also revealed some of the most common client side threats that everyone should be aware of.
Continue to the next slide for further steps...
Care to help ?
1. Learned Anything Today ? Tweet us:
2. Benefited from the presentation ? Like Coddict's Page for more!:
Thank you!
| Name: | E-mail: | ||